TCP #114: Buy vs. Build for Compliance Automation: The Decision That Stalls Most Platform Teams
There are three options, not two. Here's which tradeoffs your org can actually absorb.
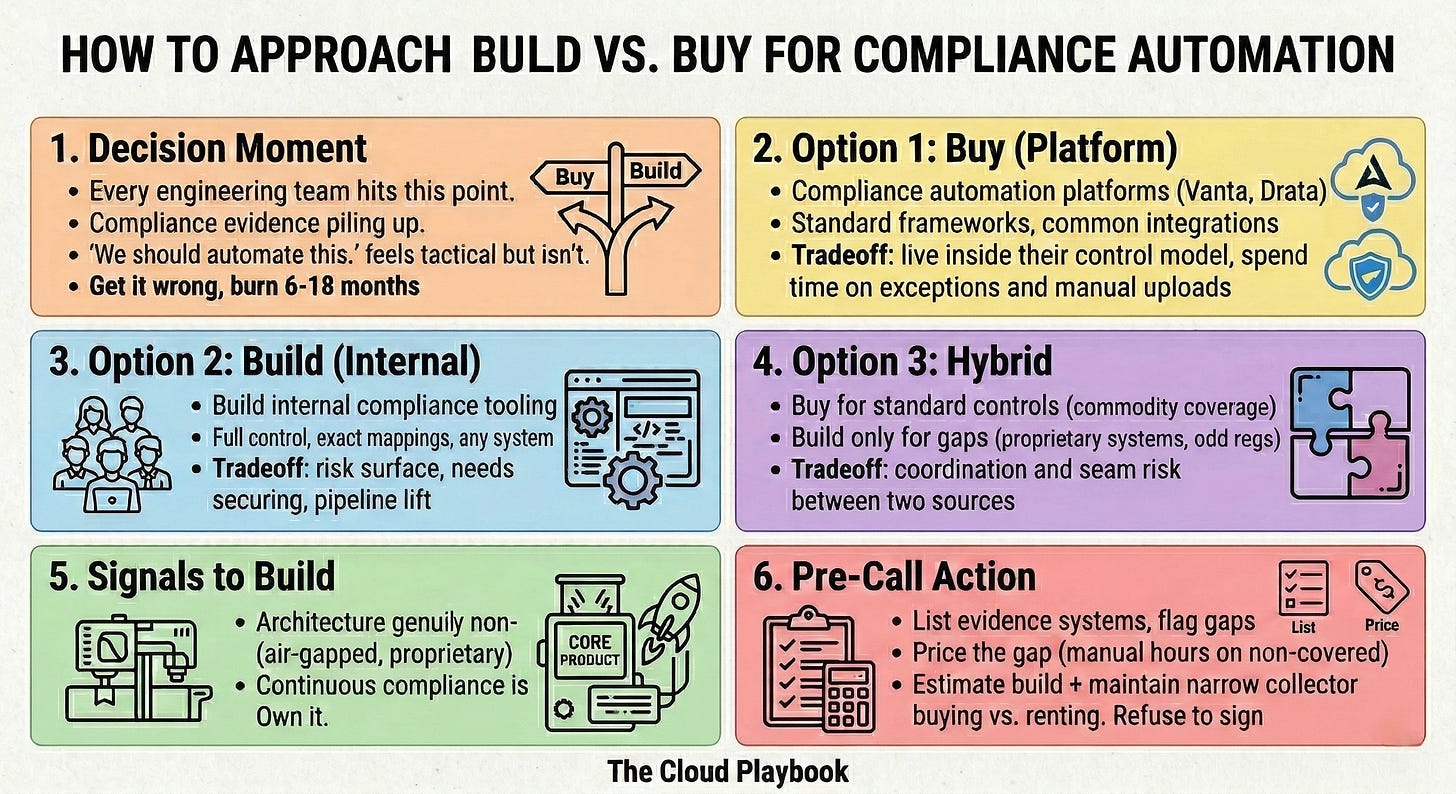
Every engineering team in a regulated environment eventually hits the same moment.
Compliance evidence is piling up. Auditors want controls you haven’t mapped yet.
Someone says, “We should automate this.” And then the room splits: buy a compliance automation platform, or build the tooling yourselves.
The decision seems tactical. It isn’t.
The wrong call costs six to eighteen months of engineering time and still leaves gaps in your audit readiness.
Building an IDP from Scratch — Live 2-day Workshop
Design and build an Internal Developer Platform that scales and gets adopted. This hands-on, 2-day workshop led by Ajay Chankramath (Founder of Platformetrics, former ThoughtWorks leader, author of Platform Engineer’s Handbook) covers platform-as-a-product thinking, cloud-native architecture, Infrastructure as Code, automation patterns, and production readiness.
Ideal for platform engineers, DevOps teams, and engineering leaders building or stabilizing IDPs.
Use discount code CLOUD40 during sign-up to get 40% off
Three Paths On The Table. Most Teams Only See Two.
There are three real options for compliance automation.
Buy a compliance automation platform. Products like Vanta, Drata, or Secureframe sit on top of your cloud infrastructure. They provide automated evidence collection, control mapping, and audit readiness dashboards. You configure integrations. They handle framework updates when the standard changes.
Build compliance tooling internally. Your platform team writes custom scripts or a compliance-as-code layer that pulls evidence from your environment, structures it for auditors, and stores it with full version history. You own every line. You control every integration.
Hybrid. Buy a platform for standard controls and automated evidence collection. Build custom tooling only for what the vendor doesn’t cover: proprietary systems, non-standard integrations, or regulatory requirements outside the vendor’s framework mappings.
Most engineering leaders treat this as a binary. It isn’t.
What Each Option Actually Cost You
Buying costs flexibility.
Commercial compliance automation tools map well to recognized frameworks: SOC 2, ISO 27001, HIPAA, and FedRAMP Moderate. They handle common integrations well. AWS, GitHub, Okta, Jira. But if your architecture diverges from what the vendor built for, expect gaps.
When your regulatory requirements don’t align with the vendor’s control library, you spend significant time on manual evidence uploads and exception management. Platform engineers end up maintaining the GRC platform instead of building a product.
That hidden maintenance cost rarely appears in any vendor’s ROI calculator.
Building costs time you don’t have — and creates a new risk surface.
Internal compliance tooling gives you full control. You can map exactly to your control set, pull compliance evidence from any system, and structure the output precisely the way your auditors want it.
But there is a cost most teams don’t price in: the moment you build your own compliance automation, that codebase becomes part of your risk surface. You need to validate, secure, and audit it as you would any other production system. Your internal compliance tooling is itself a compliance artifact.
And a credible internal automated evidence collection pipeline, with versioning, access controls, and audit trails, takes three to six months to build and maintain as a first-class capability. Most platform teams don’t have that capacity during an active audit cycle.
Hybrid costs coordination.
You get coverage where the vendor is strong and control where you need custom logic. The cost is maintaining two systems and keeping compliance evidence consistent across both.
Gaps appear at the seams. Auditors notice when evidence from your internal tooling doesn’t align with what the compliance platform reports. Reconciling those gaps during an audit is expensive and avoidable.
No option is clean. The question is which tradeoffs your organization can absorb right now.
Why I Default To Buy First And Build Only At The Edges
My recommendation is hybrid, weighted toward buy for the first two years.
Buy a commercial platform for standard framework controls. You are not going to out-engineer a vendor’s SOC 2 compliance automation mappings. They have mapped thousands of audits. You have mapped one, maybe two. Get automated evidence collection running quickly. Let the vendor handle framework updates when the standard changes.
Build for the gaps. If you run on-premise infrastructure, proprietary data pipelines, or a regulated data classification system that vendors don’t support, build a lightweight evidence collector for those specific controls. Keep it narrow. Keep it maintainable. Resist the urge to expand scope.
The reason I weigh toward buying early is simple: compliance automation is not a core differentiator. Your platform team’s time is finite.
Spending six months building an internal evidence pipeline is six months not spent on developer experience, deployment infrastructure, or reliability tooling. Buy the commodity. Build only what the market doesn’t cover.
The exception is scale. For more than 500 engineers or when operating across multiple regulatory frameworks simultaneously, vendor licensing costs and integration maintenance overhead can exceed what a well-resourced internal team would spend.
Multi-framework compliance at scale is where commercial platforms often show their seams. At that point, the build becomes economically rational and strategically worth resourcing.
Two Signals That Flip The Answer Towards Build
This framework holds when you are in your first or second audit cycle and your scope maps to a recognized framework.
Two signals change the answer.
1/ Your architecture is genuinely non-standard.
Air-gapped environments, on-premise data processing, proprietary protocols. No compliance automation tool covers these well. You will spend more time managing exceptions than building. In these environments, a commercial platform becomes a workaround, not a solution. Build.
2/ Compliance is your product.
If customers buy from you because of your compliance posture, continuous compliance is a core platform capability, not overhead. Build it. Own it. Treat it as a product with its own roadmap and dedicated engineering investment. The compliance platform decision is a competitive question when compliance is what you sell.
Everything else defaults to buy.
Run this check before your next vendor conversation:
List every system in your environment that generates compliance evidence. Flag which of your shortlisted compliance automation tools do not cover natively.
Price the gap: estimate how many engineering hours per quarter you would spend on manual evidence collection for uncovered controls.
Calculate the build cost for a lightweight internal evidence collector for just those controls, and factor in the ongoing security and maintenance overhead of owning that codebase. Compare it against the manual overhead.
That comparison tells you whether you are buying a solution or renting a workaround. The answer changes how you negotiate, what integrations you demand, and whether you sign at all.
Teams that run this analysis before signing a compliance automation platform reduce their post-implementation integration work by 40 to 60 percent.
Every team that skips it ends up in the same place: one engineer maintaining a patchwork of scripts and manual uploads six months after go-live, during an active audit.
If you want the implementation details, I go one level deeper in the paid Cloud Playbook tier:
The exact RFP checklist I use to pressure‑test compliance automation, vendors
A build‑vs‑buy spreadsheet you can plug your own engineer costs and audit scope into
Example “hybrid” reference architectures that keep vendors in their lane and your team focused on product
Whenever you’re ready, there are 2 ways I can help you:
Free guides and helpful resources: https://thecloudplaybook.gumroad.com/
Get certified as an AWS AI Practitioner in 2026. Sign up today to elevate your cloud skills. (link)
That’s it for today!
Did you enjoy this newsletter issue?
Share with your friends, colleagues, and your favorite social media platform.
Until next week — Amrut
Get in touch
You can find me on LinkedIn or X.
If you would like to request a topic to read, please feel free to contact me directly via LinkedIn or X.